Your mailbox is often the front door that hackers come knocking at to get to your companies data. It is one of the most used systems within your company and may have been already compromised without your knowledge.
Here is a 5-minute checklist you should run through on your mailbox at the start of every month, to hopefully catch any fraudsters while they sit and wait.
If anything looks suspicious or you are unsure about your inbox’s security, please give us a ring on 020 7042 6310 immediately.
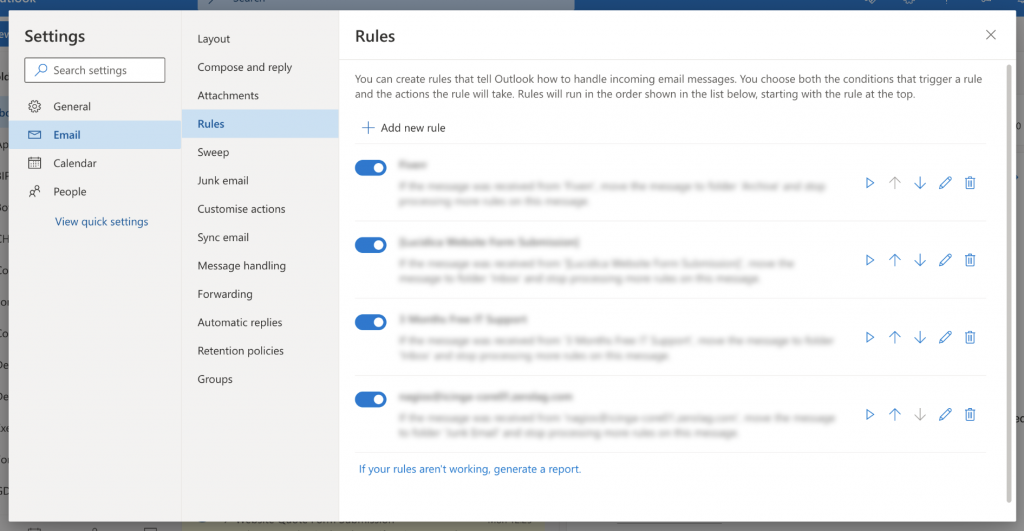
Check One: Check your rules
Within email providers, you have the ability to set-up ‘Rules’. Fraudsters most common method is to set-up a rule to forward any emails containing specific keywords such as ‘Invoice’ or ‘Payment’ to their inbox. This is to passively monster your emails, without accidentally making you aware of their presence.
Within Outlook you just need to jump into your settings and find the rules section. If you see something you do not recognise / that look suspicious then give us a ring straight away for us to have a look.
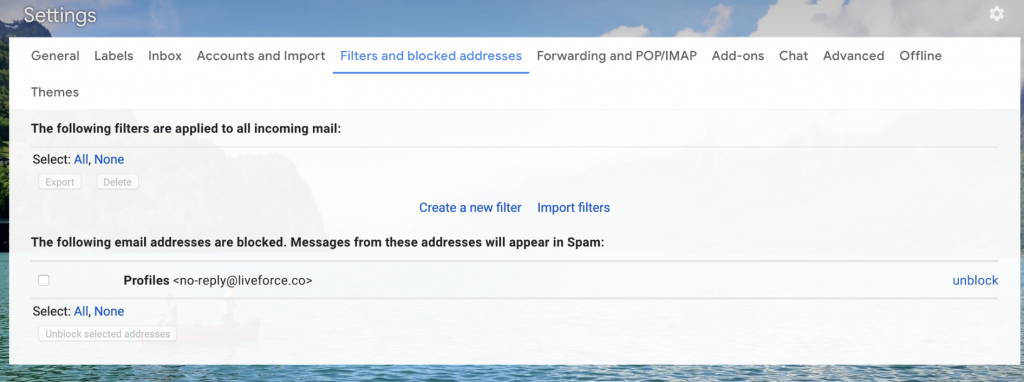
Gmail creates rules slightly differently and you may not be fully aware of how to do them. To see all the rules created, jump to the settings gear icon and view all setting > Filters and blocked addresses. From here you can see the rules. Anything that looks suspicious please give us a ring straight away.
Check Two: Update your password
If you use apassword generator, this is very easy to do and can generate a sophisticated password to use.
Anyone else already in your inbox to have to log in again, but this time without the password.
Check Three: Check haveibeenpawned
Popping your email address into haveibeenpawned.com will show you all the reported instances of third party data breaches that your email is involved in.
It is essential to know which account has been lost and to update details when a new one appears, changing passwords etc.